It’s that time of quarter again where the team here at We Fix IT are once again strengthen our cyber security measures. Being an IT company ourselves one would think we are at the for front of cyber security and we are. However, as most businesses our first focus is always our customer / clients. Meaning sometimes it can take us an extra day or two to jump onto our routine monthly maintenance checkups. This time around we had a company discussion regard 2FA inclusive of why our customers need it. How the customers currently using it are going Vs the customers currently not using it. And how it helps us as a company.
These discussions are must during our team meetings as it helps us work toward small term goals with our customers. When all of our technicians no matter their specialization understand the importance of a topic, we find it’s a lot easier to them communication the need of the service to our customers. From that discussion comes this blog. We as a small company based in the NT realized although the term 2FA is thrown around a lot many people still do not know what 2FA is, how it is used or what its used for.
So, in this blog let us give you the reader an overview.
2FA What is it?
2 FA stands for 2 Factor Authentication. It is also occasionally referred to as two-step verification or dual-factor authentication. Much like the name implies 2FA adds an additional layer of security to the authentication process in place for a service, website, application and or device. It does this by requiring the user to provide two different types of methods of information and or input to prove their identity.
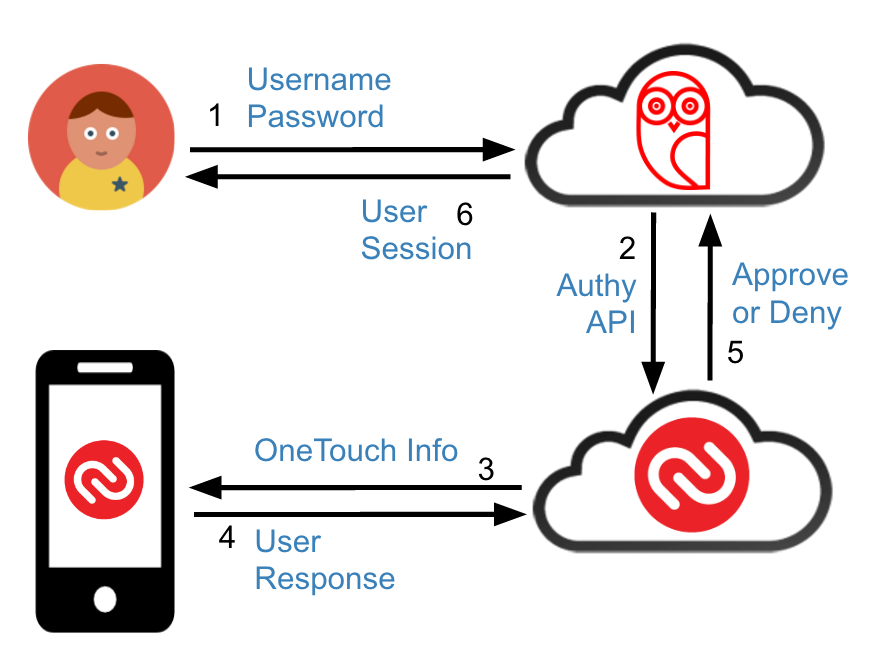
Authy an application that helps to use 2FA outlines the process of how this works on their website.
First, a user will enter their username and a password. Then, instead of immediately gaining access, they will be required to provide another piece of information. This second factor could come from one of the following categories:
Something you know: This could be a personal identification number (PIN), a password, answers to “secret questions” or a specific keystroke pattern
Something you have: Typically, a user would have something in their possession, like a credit card, a smartphone, or a small hardware token
Something you are: This category is a little more advanced, and might include biometric pattern of a fingerprint, an iris scan, or a voice print
With 2FA, a potential compromise of just one of these factors won’t unlock the account. So, even if your password is stolen or your phone is lost, the chances of a someone else having your second-factor information is highly unlikely. Looking at it from another angle, if a consumer uses 2FA correctly, websites and apps can be more confident of the user’s identity and unlock the account
Types of 2FA

It is common knowledge that if a website / application only require a username and password to allow access to an account then there is a good chance the account can be easily hacked. These types of websites and applications do not offer any type of 2FA. There are however multiple types of 2FA that can and are used today. Many of which you have probably used in your everyday life. Now in this blog we will take a look at some of the most common forms of 2 FA.
Hardware Tokens for 2FA
These are the OG form of 2FA and they can be seen in the physical forms of key fobs that produce different numeric codes every 30 seconds.
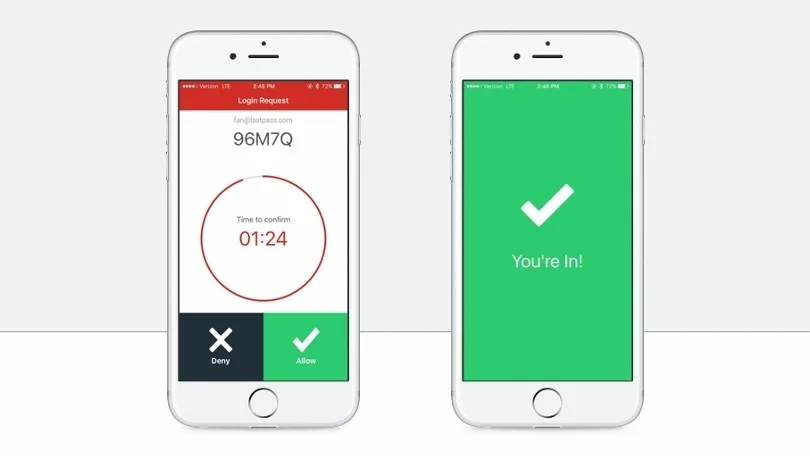
SMS Test Message and Voice Based 2 FA
This is the type of 2FA often associated with an OTP via text or call. If you use any sort of Microsoft or Google service, you are likely familiar with this 2 FA method. After signing into an account, the website or application will then send the user an OTP often with the option of getting it by text or call. Once obtained the OTP code is valid for a small amount of time in which the user needs to input it to the website or application to authenticate their identify and allow the account sign in.

Software Tokens for 2FA
The most popular form of two-factor authentication (and a preferred alternative to SMS and voice) uses a software-generated time-based, one-time passcode (also called TOTP, or “soft-token”). One of We Fix IT’s favorite applications to use for this is the Authy Application. To use this method however a user must first download and install the 2FA application on their smartphone or desktop and then set up all the needed accounts.
Other Forms of Two-Factor Authentication
- Push Notification 2FA
- Biometric 2FA

Why use 2 FA?
In the world of 2022, it is no secret that cyber security is a huge concern and that stolen, reused and weak passwords remain a leading cause of security breaches all over the globe. Sadly even though this is true and we have the reports and statistics to showcase this companies do still use passwords as the main or only method to protect their users. This is why we need 2FA. Not only has the existence of 2FA become common knowledge but using it has also become common practice in our every day lives with large businesses such as Meta, Google, Apple and Microsoft adopting the security measures.
Here at We Fix IT we use 2FA on all of our mailboxes, company software and even on our day-to-day client use website/software services. We understand the dangers of being hacking and we are actively working towards helping our customers understand those risks too. This is why we as a company encourage the use of 2FA and we help our customers set up the service to meet their needs.